State of play - Techniques used in cyber-attacks
This note provides an overview of the main current techniques used by threat actors in cyber-attacks.
- Published
- July 28, 2017
Introduction
As highlighted by a recent report, finding and exploiting zero-day vulnerabilities is getting very expensive for threat actors. Therefore, threat actors are shifting towards other attacking techniques. At the same time, such techniques enable threat actors to remain stealthy and evade available security controls. For example, in their effort to blend their nefarious activities with legitimate activities, attackers misuse legitimate software that is often used by system administrators as well. In other cases, some of the methods used leave no traces in the targeted file system. Overall following such methods allows threat actors to accomplish their goals with the minimum cost, maximum efficiency and stealthiness.
This note provides an overview of the main current techniques used by threat actors in cyber-attacks.
Attacking Techniques
According to the aforementioned report a few attacking techniques employed by threat actors have been identified. An overview of those techniques is provided below:
- Living off the land. Attackers are in pursuit of finding creative ways to operate and accomplish their goals without downloading tools and backdoors on a targeted system. This approach is called “living off the land” and refers to the misuse of pre-installed software/tools on a victim system for the purposes of an attack –especially for a targeted attack. A classic example of this category is the increasing abuse of PowerShell, which is a “task-based command-line shell and scripting language designed especially for system administrators” found in newer Microsoft Windows systems. PowerShell is often leveraged as an attacking tool for lateral movement, reconnaissance, establishment of persistence mechanisms, and exfiltration.
- Memory only attacks. These attacks refer to cases where the payload, i.e. malicious code, is executed directly in memory, leaving no evidence on the filesystem of the victim system. This type of attack is also widely referred to as “fileless attack”, although the term is often generalised to include attacks that might have a minimum footprint on the filesystem of the victim system, e.g. attacks leveraging the Windows registry. A case of a true fileless/memory only attack is the infamous “Mirai” malware, which targeted IoT devices. The malware resided in the memory of the infected IoT devices which means that a restart of those devices automatically disinfected them. As noted by the report, another recent example of a memory only attack is found in the “Wannacry” ransomworm, and specifically in the exploit it used, i.e. “EternalBlue”. Memory only attacks have also been spotted in Point-of-Sale (PoS) malware, where the malware uses ram-scraping techniques, i.e. directly access the RAM of the PoS device, to steal the card information.
- Fileless persistence methods. There are various ways attackers can achieve persistence on a system, post-infection. One example of a fileless load point technique used within Windows is the abuse of Windows registry. A malicious script can even be completely stored in the Windows registry and then get extracted and executed on the fly, as well as maintain persistence on the compromised computer.
- Dual-use tools. These tools refer to system tools and legitimate software that can be abused by attackers. Usually these tools are very powerful since they are used for administration purposes. Examples of such tools are Microsoft’s PsExec, WMI, PowerShell as well as tools that are both used by security professionals and criminals, e.g. Netcat, Mimikatz, wce etc. As a matter of fact, a tool similar to Mimikatz and PsExec/WMI were used for lateral movement in the recent NotPetya ransomware outbreak. It is quite challenging to spot anomalous behaviour when such tools are used since it is often the case that they are used in the same way by both administrators and threat actors.
- Non-portable executable file attacks. This could be considered as a subcategory of the “dual-use tools” since these types of attacks refer to the use of a malicious script executed by a legitimate tool/software, typically distributed through phishing e-mails. Examples of such attacks are: Word macros run by Microsoft word, PowerShell scripts run by Microsoft PowerPoint, weaponised PDF files, and PowerShell scripts and JavaScript in general etc.
- Injection techniques. According to another report “process hollowing is a code injection technique that involves spawning a new instance of a legitimate process and then ‘hollowing it out’, i.e. replacing the legitimate code with malware”. Moreover there are other injections techniques, such as modifying existing files that are already loaded by a system persistence mechanism, e.g. startup files, scheduled tasks, running services etc., as well as DLL injection techniques, i.e. injecting malicious code in the form of a dynamic linked library (DLL) into a running process.
How are attacking techniques and threats related?
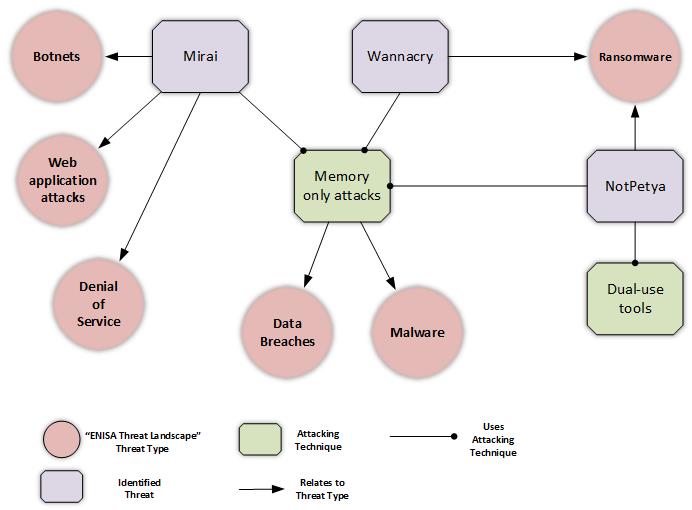
Some of the attacking techniques described above are related to known cyber threats, i.e. Mirai, Wannacry, NotPetya. Consequently, the figure below shows how these threats are related to cyber threat types defined in ENISA’s Threat Landscape. The figure provides a broader view of the general threat landscape and highlights that threats are inter-related. This perspective can be used for referring to recommendations against specific threat types, as these recommendations are provided by the respective chapters in the ETL report.
Conclusions
As described, threat actors use a series of techniques that are both stealthy and effective. Such techniques allow threat actors to bypass traditional security measures and mechanisms, e.g. signature detection methods and application whitelisting, and they are difficult to mitigate. Adopting a multilayer security approach and enhancing prevention mechanisms according to current best practices (since most of current infections originate from e-mails and the web) will reduce the possibility of initial infection, which is the most crucial part that needs to be prevented. Detecting and mitigating “fileless” and “living of the land” attacks requires a lot of contextual information, e.g. how differently a whitelisted tool is used by a threat actor as opposed to a system administrator, whether the sequential use of certain tools can raise an alarm for suspicious activity and so on. Hence, heuristic and behaviour based detection mechanisms and close monitoring of system tools are good approaches against such attacks.
The state of play of cyber-attacks implies that there will always be a mouse-cat game between threat actors and security professionals and that the latter must be in a position to keep up with current developments, adjust their defences accordingly and always apply best practices to build their defences upon a solid foundation.